“If you enjoyed this content, please support the channel by liking and subscribing – and hit the bell icon. If you feel able, then consider a regular donation via Patreon.”
Seems reasonable enough, doesn’t it? Except that we live in a world of subscriptions.
In my house we currently have Microsoft 365 (Family and E1) and Azure, Google Photos, Apple iCloud, Spotify Premium, BBC (TV Licence), Netflix, Amazon Prime (free trial for one month only), Apple TV (free trial for 3 months only), Disney (nope, just culled that), GCN (until it disappears next week) and that’s before we get to apps (Calm, Duolingo, Zoe), newsletters, podcasts, and YouTube channels.
A voluntary donation
I recently found that I was watching a lot of content from one YouTube channel in particular. And it was really helpful with one of my hobbies. So were many others, but I particularly wanted to support this one. Creating video content is time-consuming and it had helped me a lot.
So I signed up to Patreon and donated what seemed reasonable as a contribution. £1 a month for ad-free early access to new content, generally 2 videos a month.
Not much, but a contribution. After all, this is one chap videoing what he learns from his own hobby and sharing with others. It felt like a decent thing to do.
All was good and then the early access emails stopped arriving.
Not a big enough donation…
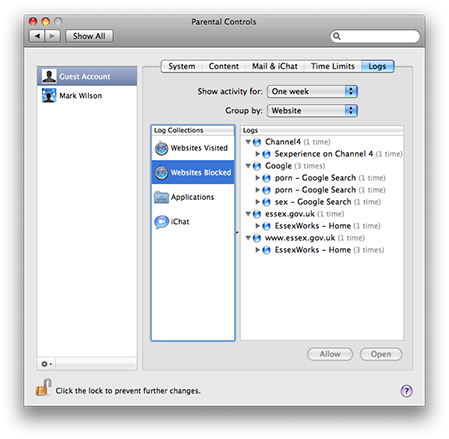
I queried with the channel producer and he, very politely, pointed out that I was not meeting the minimum contribution. At some point there was a membership structure introduced: $2 for the welcome tier; $5 for a premium level. So I upped my contribution to $2. Except it was actually £2. And Patreon added a fee on top. “$2” was charged at £2.40 (currently around $3).
I know how much effort goes into creating content. Twenty years of writing/maintaining this blog, 14 on Twitter/X, some years on Instagram and elsewhere… and creating video content is next-level…
“But it’s just the price of a coffee”
“But it’s just the price of a coffee”, you may say. Well, I drink one coffee a day… my subscriptions would add up to a lot of coffees.
£2.40 a month for a YouTube channel isn’t much money. But that’s just for two or three ad-free videos (if I watch them before they go public) – the whole of Netflix is £10.99. I don’t know how many Patreon supporters there are – but with just shy of 70,000 subscribers, 1% would be 700. Let’s say 20% pay a fiver (to the channel – so ignoring the Patreon fee) and the rest are on the welcome tier. That’s not a bad income (£1820 a month if my maths is correct). And that’s in addition to the YouTube ad revenue, which I imagine would be significant with that number of subscribers.
What’s the answer?
I don’t know what the answer is. But it feels like there are three “camps” for those producing and publishing content on the Internet in 2023:
- Altrustic individuals giving away our knowledge for free.
- People trying to turn their hobby into a living, and monetising their efforts.
- Corporates providing a service for a monthly subscription.
None of those is a bad thing. Arguably the first is unsustainable. But so is the second, if pitched at the price of a coffee a month and multiplied by many individual producers. Maybe we need micro-transactions. Or maybe we don’t. Maybe I’m just ranting and rambling but what should be the price for good, quality, ad-free content?
Featured image: generated via Microsoft Copilot, powered by DALL-E 3.

 I selected
I selected